TLDR: Blockchains can't access external data on their own. Oracles bridge that gap by fetching real-world data (prices, weather, shipment status) and delivering it to smart contracts in a verified, tamper-resistant way.
Smart contracts secure over $100 billion in DeFi total value locked. They enforce lending rules, execute swaps, and settle complex financial agreements without intermediaries. But ask a smart contract for the current price of ETH, tomorrow's weather in Kansas, or whether a container ship arrived in Rotterdam, and it draws a blank.
This is not a minor gap. A lending protocol needs ETH/USD prices to calculate collateral ratios. A parametric insurance contract needs rainfall data to trigger payouts. A supply chain contract needs shipment status to release payment. None of this data exists on-chain. Blockchains cannot natively fetch it.
Blockchain oracles bridge this gap. They source, verify, and deliver off-chain data to on-chain smart contracts, turning isolated programs into systems that interact with the real world. Oracles underpin the majority of DeFi. Understanding how they work is essential for anyone building or operating blockchain infrastructure.
The Oracle Problem
The oracle problem is not a technical inconvenience. It is a fundamental tension in how blockchains achieve their security guarantees.
Blockchains are deterministic by design. Given the same inputs, every node in the network must produce exactly the same outputs. This property makes trustless verification possible. External data sources break the model: two nodes querying a price API at slightly different times receive different results. If nodes disagree on inputs, they cannot reach consensus on outputs.
The challenge goes deeper than "how do you get data on-chain." The real question: how do you import data from inherently centralized, mutable sources into a decentralized system without reintroducing the centralized trust you designed the system to eliminate?
Three requirements make this hard:
- Data correctness - A wrong price feed on a lending protocol does not return an error. It triggers incorrect liquidations and real financial losses.
- Availability - If the oracle goes offline, every dependent contract halts. Protocols managing billions in TVL cannot tolerate feed outages.
- Manipulation resistance - If a single entity controls the oracle, it can manipulate data to exploit every consuming contract. The oracle becomes the weakest link in an otherwise decentralized system.
These requirements explain why oracles have evolved from simple data relays into complex networks with their own consensus mechanisms, economic incentives, and security models.
How Blockchain Oracles Work
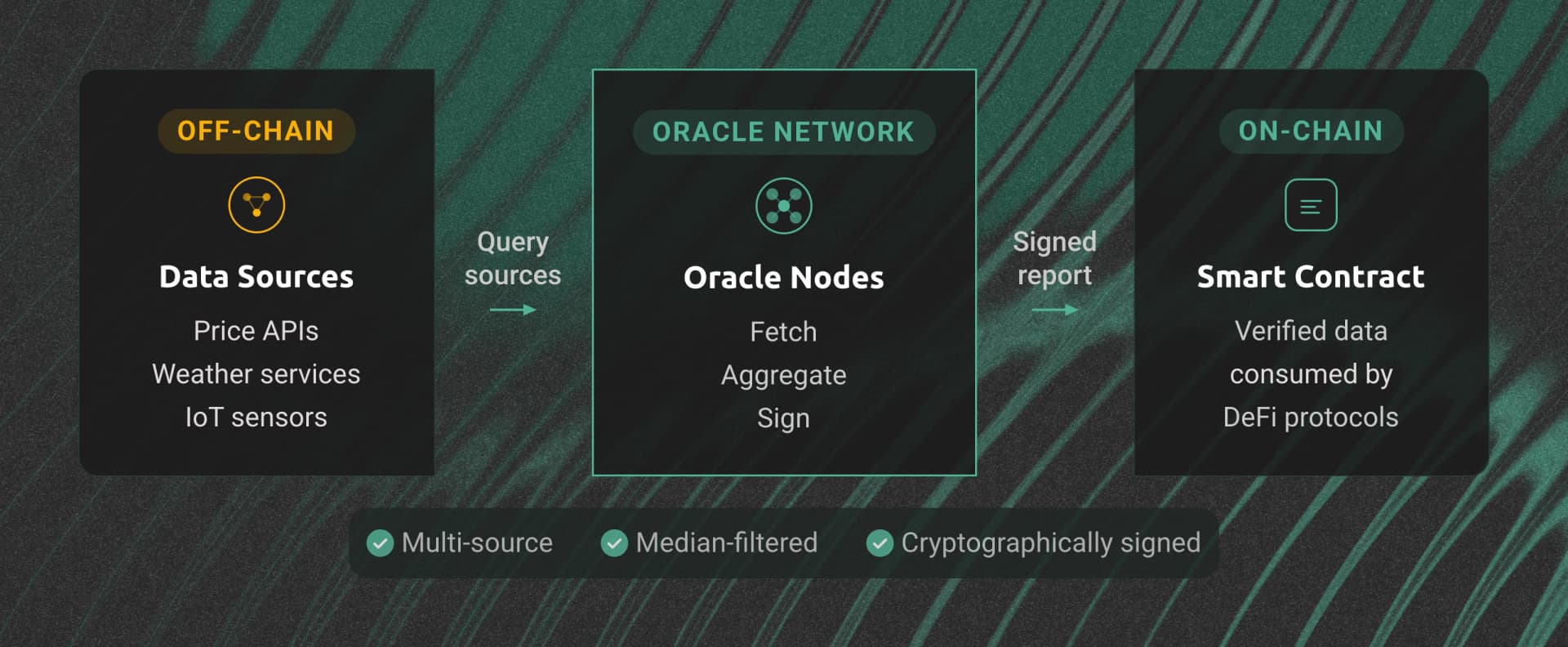
Every oracle follows the same core data flow: off-chain data source, oracle node network, on-chain smart contract. The implementation details vary depending on the delivery model.
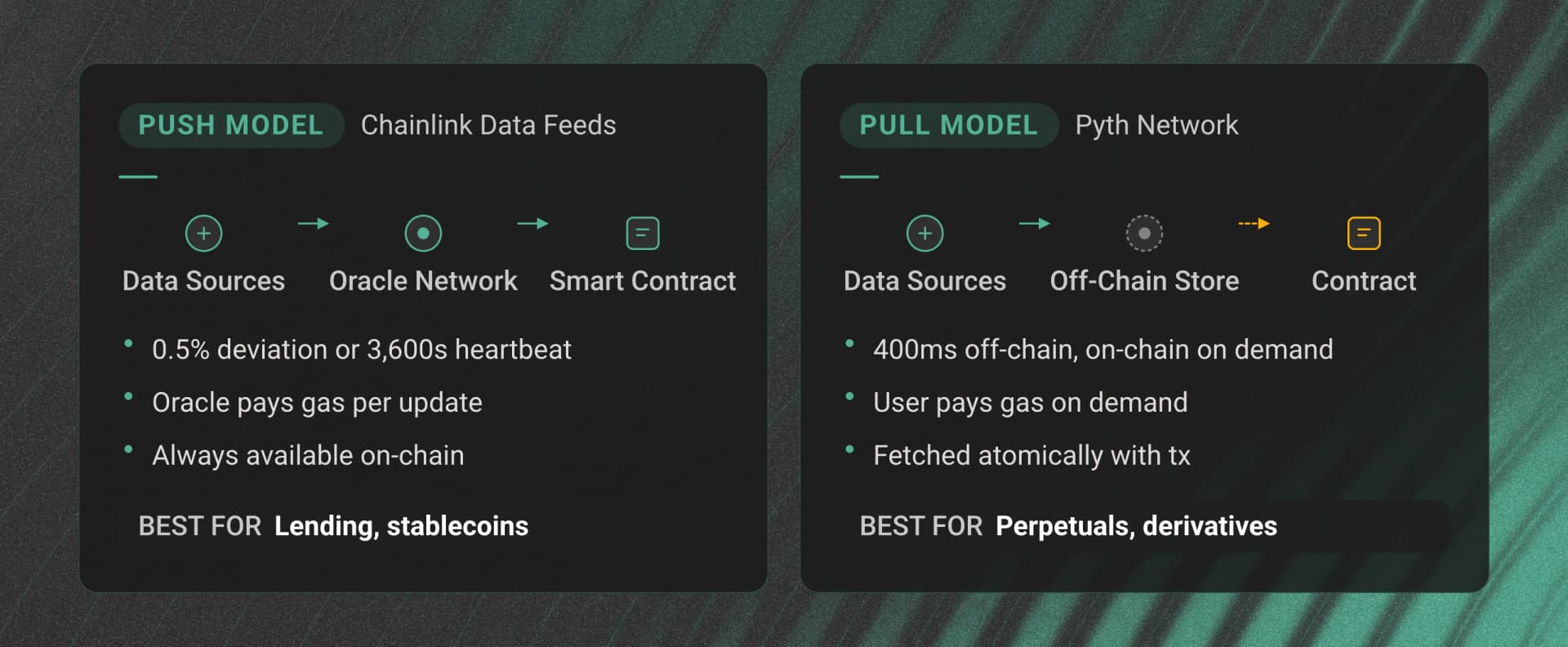
Push Model
Push oracles proactively update on-chain data based on triggers: heartbeat intervals, deviation thresholds, or both. Chainlink Data Feeds, for example, update the ETH/USD price when it deviates by 0.5% or every 3,600 seconds, whichever comes first.
The advantage is freshness. On-chain data stays current without any action from consuming contracts. The trade-off is gas cost: every update requires an on-chain transaction, even when no contract needs the data at that moment.
Pull Model
Pull oracles store data off-chain and deliver it on demand. Pyth Network pioneered this approach for financial data. Prices update every 400 milliseconds off-chain but only land on-chain when a user or contract requests them.
Pull-based delivery cuts gas costs because you only pay for data you use. The trade-off: on-chain data is not pre-populated. Your contract or a user transaction must include the price update.
Data Aggregation and Verification
Regardless of delivery model, oracle networks apply multiple layers of data quality assurance:
- Multi-source aggregation - Oracle nodes query multiple independent data sources for the same data point
- Statistical filtering - Median calculations, weighted averages, and outlier detection remove bad or manipulated inputs
- Cryptographic signing - Each oracle node signs its data submission, creating an auditable proof of who reported what
- Economic security - Staking and slashing mechanisms make dishonest reporting more expensive than the potential profit
Types of Blockchain Oracles
Oracles fall into several categories based on data direction, source, and computation model:
| Type | Direction | Example | Use Case |
|---|---|---|---|
| Input oracle | Off-chain to on-chain | Chainlink Data Feeds | DeFi lending liquidations |
| Output oracle | On-chain to off-chain | Chainlink Automation | Trigger payment via banking API |
| Compute oracle | Off-chain computation | Chainlink VRF | Provably fair NFT minting |
| Cross-chain oracle | Chain A to Chain B | Chainlink CCIP | Cross-chain token transfers |
| Software oracle | Digital data sources | Pyth Network | Real-time price feeds |
| Hardware oracle | Physical sensors/IoT | Supply chain RFID tags | Shipment verification |
Input oracles are the most common type. They deliver external data (prices, weather readings, sports scores, flight statuses) to smart contracts. Every DeFi lending protocol depends on input oracles for collateral pricing.
Output oracles work in reverse. They let smart contracts trigger off-chain actions: initiating a bank transfer, sending a notification, or activating an IoT device.
Compute oracles perform calculations off-chain and deliver verified results on-chain. Chainlink VRF (Verifiable Random Function) is the most widely used example, generating provably fair random numbers for gaming and NFT applications. Calculations that would be prohibitively expensive in the EVM run off-chain and return only the verified result.
Cross-chain oracles enable interoperability between blockchains. Chainlink CCIP (Cross-Chain Interoperability Protocol) handles token transfers and arbitrary messaging across supported chains. As the multi-chain ecosystem grows, cross-chain oracles become critical infrastructure.
Software oracles pull data from digital sources like APIs, databases, and web services. Hardware oracles connect to physical sensors and IoT devices, bridging the physical world and on-chain logic. A pharmaceutical cold-chain contract might use hardware oracles connected to temperature sensors to verify storage conditions during shipment.
Major Oracle Networks
The oracle landscape has consolidated around several networks, each with a distinct architecture and trade-off profile.
| Network | Model | Specialization | Chains Supported |
|---|---|---|---|
| Chainlink | Push (Data Feeds), Pull (Data Streams) | General-purpose, most adopted | 30+ chains |
| Pyth Network | Pull-based | Low-latency financial data | 50+ chains |
| API3 | First-party (Airnode) | Direct API provider oracles | 15+ chains |
| DIA | Community-driven | Transparent, customizable feeds | 30+ chains |
| UMA | Optimistic oracle | Dispute-resolution based | Ethereum, L2s |
| RedStone | Modular (EVM-calldata) | Gas-efficient, modular design | 30+ chains |
Chainlink
Chainlink holds roughly 70% oracle market share with over $66 billion in total value secured. Its Decentralized Oracle Networks (DONs) coordinate 900+ independent oracle nodes to deliver data across 30+ blockchains.
The product suite extends well beyond price feeds. Chainlink VRF provides verifiable random number generation. Chainlink Automation enables event-driven smart contract execution. Chainlink Functions allows custom API calls from smart contracts.
CCIP (Cross-Chain Interoperability Protocol) handles cross-chain token transfers and messaging, positioning Chainlink as both an oracle and interoperability layer.
Pyth Network
Pyth takes a fundamentally different approach with its pull-based, first-party data model. Instead of third-party nodes scraping public APIs, Pyth sources data directly from exchanges and market makers, the entities that actually generate prices. It delivers 500+ price feeds with sub-second update frequency across 50+ chains.
API3
API3 pushes the first-party concept further. API providers run their own oracle nodes (called Airnodes) directly, eliminating the intermediary layer entirely. Its dAPI (decentralized API) model creates a direct, verifiable connection between data source and smart contract.
DIA
DIA is an open-source, community-driven oracle platform with fully transparent data sourcing. Every feed's methodology and sourcing logic is publicly auditable. DIA relies on Dwellir's RPC infrastructure for multi-chain data delivery across its 30+ supported networks.
UMA
UMA introduces the optimistic oracle model. Data is assumed correct unless disputed within a challenge period. Disputers stake tokens to challenge incorrect data, and a resolution process determines the truth. This approach trades immediacy for flexibility, handling data types that traditional price-feed oracles cannot: long-form text, subjective assessments, and complex queries.
RedStone
RedStone takes a modular approach, injecting data via EVM calldata rather than writing to on-chain storage. Gas costs drop significantly compared to traditional push-based oracles. Data packages are signed off-chain and delivered only when needed, combining elements of both push and pull models.
Oracle Security: What Can Go Wrong
Oracles bridge two worlds, and that bridge is a high-value attack surface. In 2022 alone, oracle-related exploits caused over $400 million in losses across dozens of incidents.
Oracle Manipulation Attacks
The Mango Markets exploit in October 2022 showed how oracle-reported prices can be weaponized. An attacker manipulated the MNGO token price on a thin-liquidity market, inflating collateral value by roughly 45x, then borrowed $117 million against the inflated holdings. The oracle faithfully reported the manipulated market price. It was technically correct, but the price itself was artificial.
Flash Loan Oracle Attacks
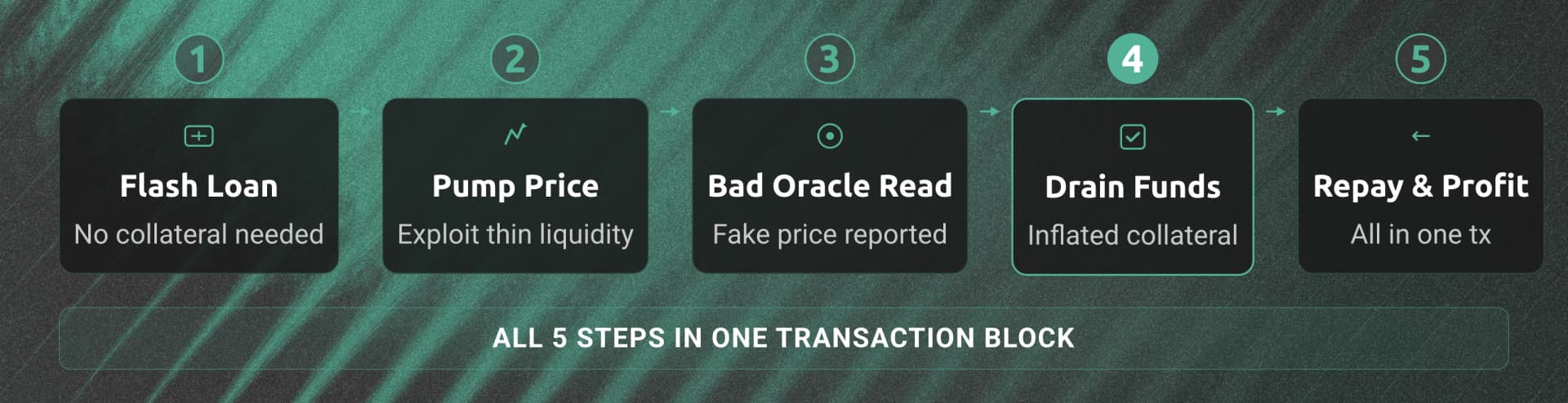
Flash loans enable a more automated attack pattern:
- Attacker borrows millions via flash loan (no collateral required, repaid in one transaction)
- Uses the borrowed funds to manipulate a token's price on a specific DEX
- A lending protocol's oracle reads the manipulated price
- Attacker borrows against inflated collateral or triggers unfair liquidations
- Repays the flash loan and keeps the profit
The entire sequence executes within a single transaction block. Oracles that rely on a single DEX as their data source are particularly vulnerable.
Centralization Risk
A centralized oracle with one data source and one operator creates a single point of failure. If the API goes down or the operator is compromised, every protocol consuming that feed is affected. This is the same centralization risk blockchains were designed to eliminate.
Mitigation Strategies
Protocols that have avoided oracle exploits share common practices:
- Multiple independent data sources - Aggregate across several sources rather than relying on a single DEX or API
- Time-weighted average prices (TWAP) - Use price averages over time windows rather than spot prices, making single-block manipulation economically impractical
- Circuit breakers - Set maximum deviation thresholds. If a reported price moves more than 10% from the last known good value, pause the protocol
- Decentralized oracle networks - Manipulating a single data source is straightforward. Manipulating Chainlink's 900+ node network is economically impractical
- Infrastructure reliability - Oracle nodes depend on RPC endpoints to read on-chain state and submit transactions. Unreliable infrastructure means delayed updates, missed liquidations, and stale data
Why Infrastructure Matters for Oracles
The security section above listed infrastructure reliability as a mitigation strategy. That point deserves expansion, because oracle nodes are middleware with hard dependencies on both sides of the bridge.
Every oracle node needs RPC endpoints for three critical operations: monitoring on-chain requests and events, reading contract state, and submitting data update transactions. If any of these fail or slow down, data delivery degrades.
Latency is consequential. A 500ms delay in an oracle price update during high volatility can mean the difference between a successful liquidation and protocol bad debt. For Pyth's sub-second update model, the RPC infrastructure handling read-write cycles must keep pace.
Multi-chain deployments compound the challenge. Chainlink operates across 30+ chains. Pyth reaches 50+. Oracle operators need reliable node infrastructure across every chain they serve. Managing separate RPC providers per network creates operational complexity and increases outage surface area.
This is why DIA chose Dwellir's multi-chain RPC infrastructure for primary and backup data delivery across its 30+ supported networks. For any team running oracle nodes or building oracle-dependent protocols, infrastructure choices directly impact data freshness and system reliability.
Getting Started with Oracles
If you are building a protocol that consumes oracle data, integration is straightforward. This Solidity example reads the latest ETH/USD price from a Chainlink Data Feed:
// SPDX-License-Identifier: MIT
pragma solidity ^0.8.7;
import "@chainlink/contracts/src/v0.8/interfaces/AggregatorV3Interface.sol";
contract PriceConsumer {
AggregatorV3Interface internal priceFeed;
/**
* Network: Ethereum Mainnet
* Aggregator: ETH/USD
* Address: 0x5f4eC3Df9cbd43714FE2740f5E3616155c5b8419
*/
constructor() {
priceFeed = AggregatorV3Interface(
0x5f4eC3Df9cbd43714FE2740f5E3616155c5b8419
);
}
/**
* Returns the latest ETH/USD price.
* Price is returned with 8 decimal places.
*/
function getLatestPrice() public view returns (int) {
(
/* uint80 roundID */,
int price,
/* uint startedAt */,
/* uint timeStamp */,
/* uint80 answeredInRound */
) = priceFeed.latestRoundData();
return price;
}
}
The latestRoundData() call reads the most recent aggregated price from Chainlink's on-chain contract. By the time your contract reads it, the price has been sourced from multiple exchanges, aggregated across independent oracle nodes, and written on-chain with cryptographic proofs.
For production deployments, add staleness checks. Verify the timeStamp returned by latestRoundData() is recent enough for your use case. A feed that has not updated in hours may indicate an oracle outage. Your contract should handle that gracefully rather than acting on stale data.
If you are running oracle nodes rather than consuming feeds, the priorities shift to infrastructure. Low-latency, high-availability RPC endpoints across every chain you serve are non-negotiable. A node that misses transaction submission windows degrades the entire network's data quality.
Conclusion
Blockchain oracles solve one of the most fundamental limitations in smart contract design: connecting deterministic, isolated systems to a non-deterministic world. From DeFi price feeds securing billions in collateral to parametric insurance contracts paying out on weather events, oracles are the infrastructure layer that makes smart contracts practical.
The ecosystem has matured from simple centralized data relays into sophisticated decentralized networks with multiple delivery models. Push vs pull, first-party vs third-party, optimistic vs aggregated. Each architecture carries trade-offs in cost, latency, security, and trust assumptions. Understanding these trade-offs is essential for any team building protocols that depend on external data.
What remains constant across all oracle architectures is the dependency on reliable node infrastructure. Oracle data is only as good as the RPC endpoints delivering it. For teams building oracle-dependent applications or running oracle nodes, explore Dwellir's multi-chain RPC endpoints across 50+ supported networks, or contact the Dwellir team to discuss your infrastructure requirements.


